International Revenue Share Fraud
Is there a cure?

Actually there is a cure for I.R.S.F. No, it is not in any unique box you can buy from any Antifraud Vendor. That is why no Telecom company has solved the problem! In reality, without everyone stepping outside of the box, you will not see it either…although it has been under your nose all along.
First let us examine the structure of a telecom company’s revenue assurance department. Then we will examine the nature of I.R.S.F and why you have never been able to stop this fraud.
Revenue Assurance Department
Most RA officers are put into a box to work, just as are other department heads. He is expected to stop fraud. However, he has very little or no control over…
- Account authorization
- Roaming accords, negotiations and audits
- Distributor allocations, negotiations and contracts
- Commercial installation controls
- Sub-contractor surveillance/security
- Internal officer personnel
- Accounting
- Legal
So, if the RA Officer is only able to work on fraud after it is committed, how does he function?
The RA officer is expected to detect fraud and since he usually has less money budgeted for his department than his own annual salary; he must wait for a vendor to come to him or find a vendor, who sells a product that promises to:
- Detect sim-box fraud
- Analyze CDR’s
Once he does this, then he brings in his boss, usually a director to listen to a presentation. Then if approved, they ask for a quote and a business case is made. If the imaginary numbers presented make good sense, then they ask the vendor to give a demo, sometimes called a Proof of Concept (POC). Assuming it gives the desired results, usually about 30% capture rate, they buy it and put it into operation.
I can assure you without any reservation that this does not work on IRSF. In fact there is no guarantee that this works well on sim box detection either; but that is another speech.
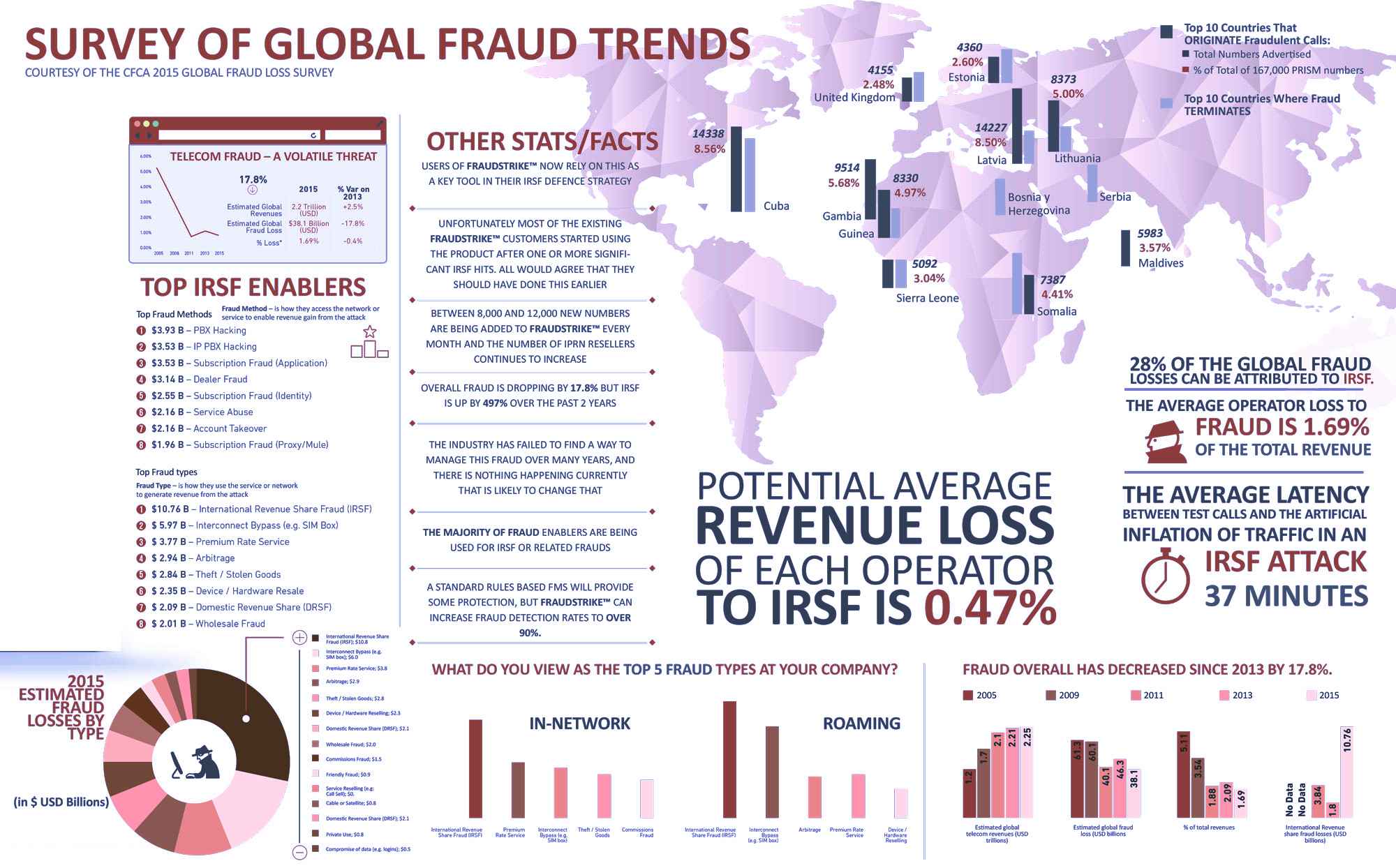
What is IRSF
Since you are already in Revenue Assurance or you would not be reading this, I will not explain what it is, rather how it exists. So, what are the various elements involved in perpetrating IRSF? After you see this, you will know why it has always been impossible to mitigate losses from IRSF.
- Rigid corporate structure: Criminals can only be successful and will only target telecom companies who have a rigid hierarchy wherein the Revenue Assurance department is limited to operating within the standard job/department description relative to most all telecom companies.
- Internal Support: Criminal cannot make major frauds nor maintain the frauds without inside help. This can be from employees or subcontracts or partner MVNO’s or roaming partners (or their insiders).
- Someone must authorize a sim card. Or
- Someone must give the criminal the PBX location and/or password/login, or
- Well-Funded: IRSF can be perpetrated on a small scale with only three people using three hacked droid phones or one PBX plus two droid phone. And over a weekend, either of these can steal between $43,000 and $800,000(PBX). However, large-scale IRSF is perpetrated by well-funded companies and organizations who invest a great deal in setting up the operation. Many criminals invest between $50,000 minimum and $400,000 in a single operation. And often it is in collusion with another major telecom company. One operation a few years ago against most Carriers in Mexico was in Cancun. The criminal group purchased 300 Hypermedia gateways (960 channels) plus switches, routers, racks, etc. Their NOC/NODE was telco grade class 4 with fully trained technicians 24/7. They operated for more than a year before it got too hot and they closed down. Their startup funding was over $5,000,000!
The Cure
The cure or solution is a combination of cutting edge technology plus management changes.
- NAC must be cleared, redesigned and controlled. And this must be facilitated by a outside contractor under the auspices of Senior Management and Revenue Assurance.
- A detection software which both analyzes and learns (AI) as it processes data must be deployed.
- This new platform must sync with the NAC, accounting, roaming and revenue assurance department to filter all data and find the frauds.
- The platform must be able to define and write its own policy management rules to either be automatically enforced, or manually enforced.
- Finally, this platform must predict where new fraud will transpire and be prepared to recognize it and act.
INTRODUCING THE SHIELD – DEATH STAR
The newest of cutting edge technology today. And it does it all. In fact, it not only annihilates:
- IRSF
- Sim-Box Fraud
- PBX Fraud
- Spoofing
- VoIP Fraud
- OTT Signal Cloning Fraud(prevent Whatsapp streaming)
- IMEI Change Fraud
- Internal Billing Fraud
- Cyber Security
- Account Authorization Fraud
Plus, it puts it all in graphics and user interfaces which are to help both Revenue Assurance officers and Upper Management see where the money goes.